Plugins review
Developing a Livestorm plugin requires no prior approval of any kind. Simply install the SDK and you will be able to develop plugins that will be scoped to your organization.
Your plugin may need a review in any of the following cases:
- You want to publish your plugin publicly to Livestorm's apps marketplace
- You encounter errors due to the Same Origin Policy
- You need to use private APIs
Just like any other Livestorm command, submitting a review request requires you to have the CLI installed
The review process
To submit a review request, simply use the livestorm review command.
This command will guide you through the few steps required to submit your review.
Thereview command
Here's what this command will do:
- Ask the purpose of your review
- Ask your email so that we can communicate with you (only for the scope of this review)
- Bundle and publish your plugin (just to be sure to be reviewing the latest revision)
- Send the review request and notifies us to check out your plugin
How we review plugins
In general, reviewing a plugin is a combination of security and UI/UX verifications.
By reviewing the plugin code we ensure that there is no security breach or major GDPR-related issues.
By installing the plugin on our organization, we test and ensure that the plugin complies with our visual, functional and ethical guidelines.
Based on this, we decide to either approve or deny the review request, which will trigger the corresponding workflow depending on the purpose of the review. In any case, you'll be notified by email.
Submit your plugin to the Marketplace
Before submitting your plugin for a marketplace validation, please read ourtechnology partner terms and conditions. By submitting your plugin for a review, you agree upon the above terms.
By choosing the "I want to publish my plugin to Livestorm Marketplace" option in the livestorm review command, you enter a slightly different review process.
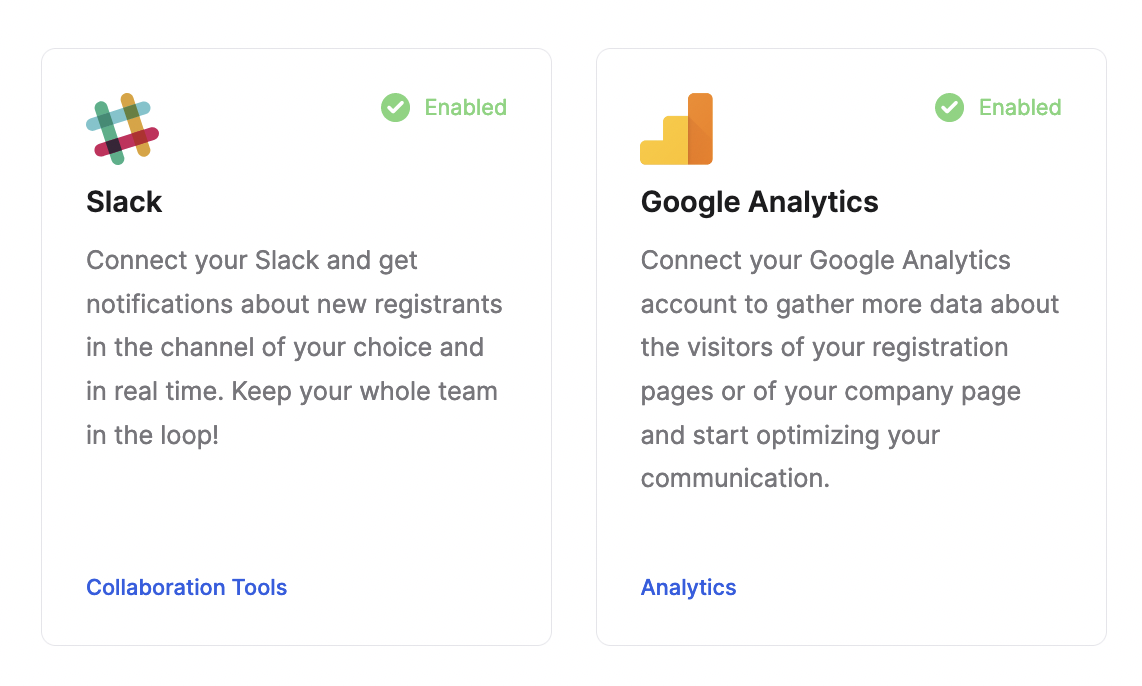
Publishing to the marketplace implies that your plugin will be visible publicly by any Livestorm user.
This means that your plugin will need a few assets to be displayed properly:
- A logo
- A public title (translated)
- A description (translated)
To add those assets alongside your review, edit your environments.json and add a metadata property to your environment, matching the following format:
{
"production": {
"apiToken": "xxx",
"name": "my-plugin",
"metadata": {
"logo": "https://logourl",
"translations": {
"title": {
"en": "Emoji Reactions",
"fr": "Emoji Reactions"
},
"description": {
"en": "This is an amazing plugin",
"fr": "Voici un plugin extraordinaire"
}
}
}
}
}
We recommend uploading your logo beforehand using the livestorm asset command, and then provide its hosted URL in thelogoattribute so that its URL will never cease to exist.
To preview your metadata, go to the marketplace and check out the visuals associated with your plugin :
If you need help creating a logo, writing translations, or providing any of the required assets, feel free to send and empty json file {} and specify that you need help when prompted during the livestorm review command. We'll reach out to you via email.
Please note that sending a plugin to the marketplace requires you to have an environment namedproductionin yourenvironments.jsonfile
The Same Origin policy
Same Origin policySince plugins are developed within null-origin iframes, they do not share the origin of the parent Livestorm document.
This is a security measure that prevents plugins from interacting with the parent document.
Some browser features or third-party integrations might not work due to this limitation and raise errors such as :
Sandbox access violationThe frame being accessed is sandboxed and lacks the "allow-same-origin" flag.
To get the allow-same-origin flag on your plugin templates you can use the livestorm review command and specify that you need the flag.
If approved, your plugin will automatically gain the allow-same-origin flag and your error will disappear.
If you want to bypass this limitation temporarily on your own machine (to be able to continue developing your plugin without waiting for approval), simply launch Chrome with the flag--disable-web-security.
Updated over 1 year ago